Learn about DMARC, SPF, and DKIM
Welcome to DMARCPal's Learn blog. Check our posts to discover and learn more about DMARC, SPF, DKIM, and how to get the most value of your DMARCPal subscription.
The first few DMARC aggregate reports usually feel harmless.
Then a domain starts sending more mail, more receivers participate, forwarding paths multiply, and suddenly the rua mailbox turns into an operations problem instead of a reporting checkbox.
At that point the question is not "how do w...
Warm-up is really a trust-building exercise.
The technical side matters, but the bigger question mailbox providers are answering is simple: does this sender look predictable, wanted, and well-controlled as volume increases?
That is why teams sometimes publish SPF, DKIM, and DMARC correctly, the...
PSD DMARC is one of those DMARC topics that sounds niche until you run into a domain space where it matters.
If you only manage a normal domain like example.com, you may never need to publish anything specifically for PSD DMARC. But if you troubleshoot mail in regulated namespaces, branded suffi...
Teams often talk about "separating transactional and marketing mail" as if it were a single switch.
It is not. In practice, there are three different separation levers:
- IP separation
- DKIM domain separation
- visible From-domain and subdomain separation
Those levers overlap, but they do n...
If you are planning a BIMI rollout, the main mistake to avoid is treating it like a logo-upload project.
BIMI is really the last layer in a chain that starts with stable email authentication, moves through DNS and HTTPS hosting, and only then reaches logo display. If any earlier piece is weak, the...
BIMI and DMARC are closely related, but they do different jobs.
DMARC is the policy and alignment layer that tells receivers whether mail claiming to be from your domain is authenticated well enough to trust. BIMI is the branding layer that can let participating mailbox providers display your l...
BIMI stands for Brand Indicators for Message Identification.
At a practical level, BIMI lets a domain owner publish the logo it wants participating mailbox providers to display next to authenticated mail. When it works, the recipient sees the brand logo in the inbox or message view instead of on...
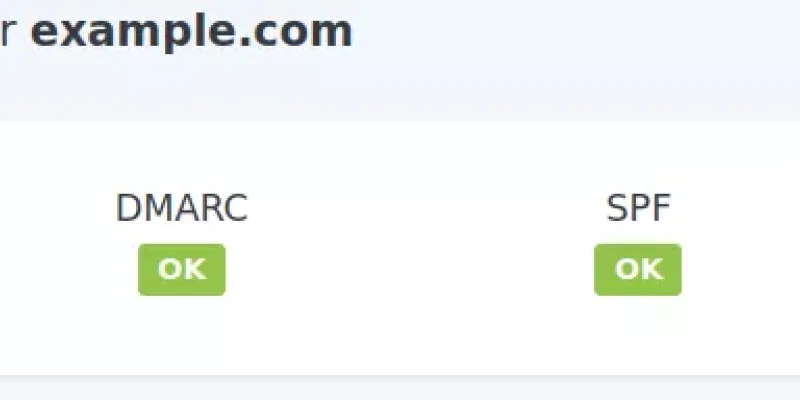
Publishing DMARC is an important milestone, but it is not the finish line for deliverability.
After SPF, DKIM, and DMARC are in place, mailbox providers still make inbox and spam decisions based on sender reputation, user complaints, list quality, traffic consistency, and overall message quality.
...Some DMARC mistakes fail loudly. Most do not.
The dangerous ones are the records that look published in DNS, maybe even show up in a quick TXT lookup, but are unusable enough that receivers treat them as if no real enforcement policy exists.
That is how teams end up saying "we already publishe...
DMARC reports are usually less sensitive than people fear, but not so harmless that they should be thrown into an ordinary shared mailbox and kept forever.
That is the practical middle ground.
Aggregate rua reports are mostly domain-level telemetry. They tell you which sources claimed to sen...
ruf is still part of DMARC in 2026, but it is no longer something most domain owners should treat as a core visibility channel.
The short reason is simple: failure reports can be very detailed, privacy-sensitive, high-volume, and inconsistently sent. That combination makes them useful in narrow...
If a domain moves to p=quarantine or p=reject before it knows every legitimate system using its visible From domain, the breakage is usually self-inflicted.
That is the real reason to spend time in p=none first. It is not because monitoring feels safer in the abstract. It is because DMARC...
The p= tag is where DMARC stops being just a reporting mechanism and starts becoming a delivery policy.
It tells participating receivers what the domain owner wants done with messages that fail DMARC. That last part matters more than many guides make clear: p=none, p=quarantine, and p=rej...
Teams usually discover the limit of DMARC right after doing the hard part correctly.
They lock down SPF, DKIM, and DMARC on example.com, move toward enforcement, and cut off direct spoofing against their real domain. Then a phish shows up from examp1e.com, example-support.com, or an internat...
Microsoft 365 email authentication gets confusing faster than it should, mostly because every tenant has at least two domain stories happening at once:
- your real public domain, like
example.com - the tenant's built-in
.onmicrosoft.comdomain
And those two do not behave the same way.
T...
DKIM selector rotation sounds simple until the first real outage: mail starts failing DKIM checks, DMARC pass rates dip, and suddenly everyone is asking which key is actually live.
The good news is that this is very manageable with a repeatable process.
This guide focuses on practical operations...
ARC gets misunderstood in two opposite ways.
Some teams treat it like magic and expect arc=pass to undo every SPF, DKIM, and DMARC failure. Other teams ignore it completely and miss useful context during forwarding incidents.
The practical middle ground is simpler: ARC is a trust transport f...
If your team forwards mail through gateways, list servers, or security services, this scenario is probably familiar: SPF fails, DKIM fails, DMARC fails, and yet the message is still clearly legitimate.
That is exactly where ARC becomes operationally useful.
But the part that causes confusion is...
If ARC headers still look like random noise during an incident, that is normal.
Most teams first care about ARC when a forwarded message is obviously legitimate, but DMARC still fails somewhere downstream. At that point, reading cv=, i=, d=, and s= quickly is what separates a five-minute d...
Short answer: deploy ARC where mail is actually being forwarded or transformed.
That usually means the forwarder, mailing list, or gateway should do the sealing. The final receiver should do validation and trust decisions. A domain owner that only sends direct mail usually does not get much benefi...
If DMARC looked perfectly healthy yesterday and suddenly starts failing for forwarded messages or list traffic, you are not looking at a weird edge case. You are looking at a normal email path.
Forwarders and mailing lists are exactly where DMARC gets interesting, because they change message paths...
If ARC still feels fuzzy, that is completely normal.
Most admins first meet ARC while debugging a very practical problem: "this message is legitimate, but DMARC failed after forwarding." ARC exists for exactly that kind of path.
ARC stands for Authenticated Received Chain. It is defined in RFC...
When DMARC fails, the DNS record is often blamed first.
In practice, the fastest path to the real cause is usually the message header, specifically the Authentication-Results line. That one line tells you what the receiver believed about SPF, DKIM, and DMARC at evaluation time.
If this still f...
If a domain does not send email, that domain should still have an email authentication posture.
That sounds odd at first, but parked or unused domains are frequent spoofing targets precisely because nobody watches their mail flow. Attackers can forge From: yourbrand@example.com from a quiet doma...
pct looks like a comfort knob.
Set p=quarantine; pct=10, wait a bit, then raise it to 25, 50, 100. On paper that sounds controlled and safe.
In production, it is useful but not magical. Some receivers treat pct as a hint, sampling details vary, and policy behavior is not guaranteed to be...
Sometimes DMARC reports need to go somewhere other than the domain in the From address. That is common when reports are collected by a shared mailbox, a central security team, or an external processor such as DMARCPal that receives and organizes reports. DMARC allows that, but only after the destina...
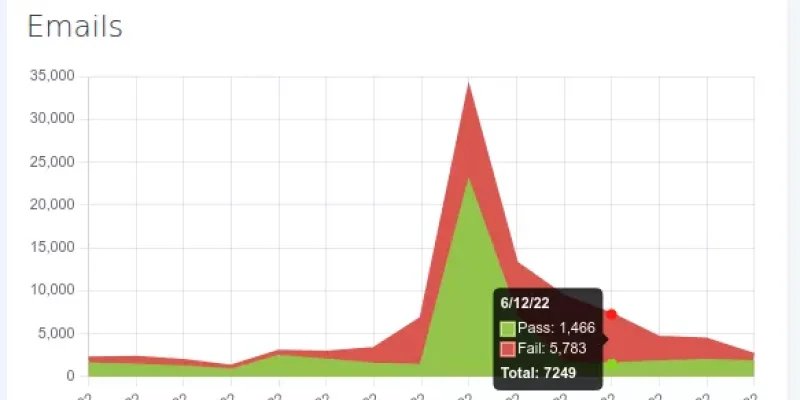
At some point every DMARC rollout hits this exact moment:
"The DNS record is published... now what?"
The answer is reporting. Specifically aggregate DMARC reports (rua) sent as XML files.
This is where DMARC stops being a checkbox and becomes operations: figuring out who is sending as exa...
DMARC reporting is where the whole thing stops being theoretical.
If DMARC is the policy you publish in DNS, DMARC reports are the receipts: mailbox providers telling you what they observed when mail claiming to be from example.com hit their systems.
Those reports are what let you answer que...
If email keeps landing in Gmail's Promotions tab, the instinct is to look for a technical switch: "maybe DMARC fixes this".
DMARC is worth doing, but it's not that switch.
DMARC is about whether a message is allowed to claim a domain in the visible From: address. Gmail uses that (and SPF/DKI...
If email from a perfectly legitimate system suddenly starts landing in spam (or bouncing), it usually isn't because "deliverability is mysterious".
It's because mailbox providers have been steadily raising the floor for what counts as a well-behaved sender.
This isn't just about inbox placement,...
“Apex domain” is one of those phrases that sounds more exotic than it is.
In day-to-day DNS work, the apex is simply the top name of the zone being edited. If the DNS zone is example.com, then the apex is example.com itself (sometimes shown as @ in DNS dashboards). If the zone is news.exa...
DMARC gets talked about like a single switch you flip for a domain.
In reality, most domains are a small ecosystem:
- the apex (
example.com) where people type addresses and expect mail to "just work" - a handful of subdomains used for actual sending (
news.example.com,billing.example.com,...
It only takes one look at a real DMARC record to realize why people hesitate.
p, sp, pct, rua, ruf, fo, ri, rf...
It's not hard once it clicks. It's just that every tag looks equally important when you're new to it, and DNS is an unforgiving place to experiment.
This is a fiel...
If you've ever stared at a DMARC report thinking "but SPF is passing... why is DMARC failing?", you've already met identifier alignment.
Alignment is one of those things that sounds like an academic detail until it bites you in production. Then it becomes the entire story.
In DMARC terms, what...
Forged emails are a growing concern for personal and business communication. With the ease of sending fake emails that appear to come from a different source, it's essential to be aware of the dangers and take steps to prevent them.
This blog post will explore the reasons why it's so easy to send ...
DMARC is a protocol for email authentication. It allows domain owners to specify how email from their domain should be authenticated. But some domain owners may get too many reports and want to stop receiving them.
Some people may want to stop receiving DMARC reports because they are getting too m...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
Mistakes can happen.
An updated DKIM selector record may be missing a semicolon. Someone in a rush could mistype t...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
In the previous steps of the 5-Stages DMARC Setup process we got to know more about the domain email traffic pattern...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
Depending on the volume of emails you send, how old your domain is, and how much exposure it has, your DMARC reports...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
The objective of this stage is to collect data so we get to know how email from the domain flows and, in parallel, m...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
Planning and controlling the DMARC deployment process is crucial to avoid problems and questions down the road that...
This is a continuation post covering a process to setup DMARC on active domains. Visit A (sane) DMARC setup process for busy email domains to know more about this post series.
Here is a brief overview of the DMARC setup process we will be covering in this post series:
The 5-Stages DMARC Se
...DMARC is great. It allows you to publish your email sending policies, and those are used to prevent phishing emails using your domain. On top of that, it also provides reporting facilities that give you insights on your email delivery.
Implementing DMARC on new domains is straightforward. You just...
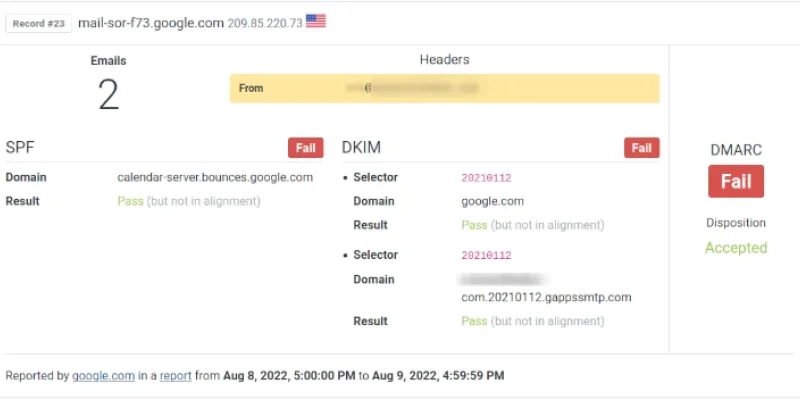
If you are a Google Workspace user and use Google Calendar, you may have noticed some DMARC fails on your DMARC reports.
Here’s a sample record extracted by DMARCPal Record Explorer showing the issue:
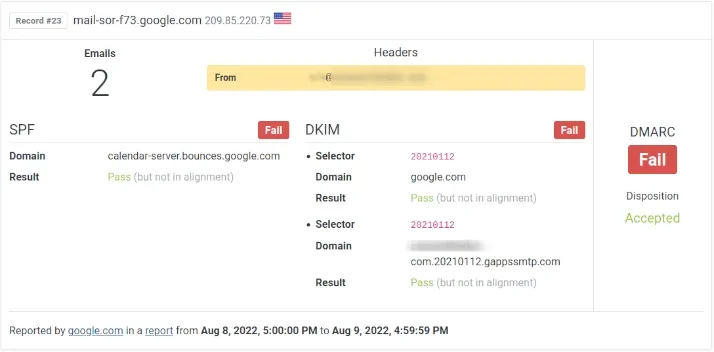
The problem is caused by Google sending those emails from domains that don’t align with the...
Not a long time ago, Internet email was based on trust. Trust on the servers, trust on the people running the servers.
Trust that who you see in an email “From” is really who wrote that message.
As of 2020 about 3+ billion forged emails are sent in a day, and it is safe to say (no pun intended...
This happens more often than we think: an employee receives an email from his boss requesting him to do something.
It might be something as simple as requesting a document.
Or more serious, such as the credentials to the company’s social media accounts. Or to transfer several thousand dollars to...